vSphere 6.5 released with lot of new features that most of them were waiting for. vSphere 6.5, the latest version of its industry-leading virtualization platform. This new release of vSphere features a dramatically simplified experience, comprehensive built-in security, and a universal app platform for running any app. I agree with the feature sets, availability and Scalability features of vSphere 6.5. What about Security?
I would say vSphere 6.5 is a turning point in VMware infrastructure security. Security in Virtual infrastructure is always been an big challenge due to its scale of 1000’s of Virtual machines. With the latest release there are lot of new features are added to improve the vSphere 6.5 Security features.
What’s New in vSphere 6.5 Security for Virtual Machines
Virtual Machine Encryption
New vSphere 6.5 Security feature called VM Encryption, Virtual Machine Encryption happens at hypervisor level and not in Guest OS. It is also not rely on Guest operating system type too. You need apply the encryption policy to the Virtual machine using the Virtual Machine storage policies. Once encryption policies are applied to the VM, VMDK and VM home files will get encrypted. VM Encryption is policy drive and managed via policies. Since Encryption is not happening at Guest OS level, Guest don’t have access to the Keys.
Key Management is based on the industry standard, KMIP 1.1. In vSphere 6.5 Security, vCenter is a KMIP client and works with a large number of KMIP 1.1 key managers. This brings choice and flexibility to customers. VM Keys do not persist in vCenter.
Graphic Thanks to VMware.com
When you applied the encryption policy to the Virtual machine, Randomly generated keys will be created for each virtual machine and also that key is also encrypted with the key from the Key Managers.
When Encryption enabled virtual machines gets powered on, vCenter server as a KMIP client retrieves the key from the key manager and send that down to the VM encryption module in the ESXi hypervisor and unlocks the key.With that, All IO coming out from the virtual SCSI device goes through the hypervisor encryption module before it hits the storage module.
vMotion Encryption
vMotion Encryption also needs to be enabled per-VM level. When vMotion Encryption enabled Virtual Machine is migrated using vMotion, vCenter Server will randomly generate 256-bit key and the generated Key will be added in migration specification sent to both ESXi hosts participating in the Virtual Machine migration. During vMotion, All the data going across the network are encrypted with the help of randomly generated key by vCenter Server. Key generation for vMotion Encryption is only performed by vCenter Server not performed by any Key Managers.
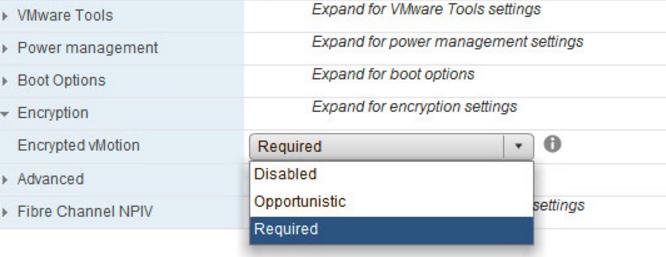
There are 3 types of vMotion Encryption options:
- Disabled – vMotion Encryption not Enabled
- Opportunistic – It uses encrypted vMotion, if source and destination ESXi hosts supports it. If destination ESXI host doesn’t support, It performs the normal vMotion operation
- Required – It only allows the encrypted vMotion. If the source or destination ESXi host does not support encrypted vMotion, then the vMotion operation will fail.
Virtual Machine Secure Boot
Virtual Machines should be configured to use EFI Firmware and also Secure boot option need to be enabled for Virtual machine to use SecureBoot feature. It is simple to enable and use. Once Secure Boot is enabled on Virtual Machines, It will allow only to load signed drivers into the Virtual Machine. Virtual Machine Secure Boot work with Windows or Linux operating systems.
I am sure you are impressed with the vSphere 6.5 security features. I hope this is informative for you. Thanks for Reading!!. Be social and share it in social media, if you feel worth sharing it.
vSphere 6.5 Related Posts:
What’s New with VMware vSphere 6.5?
vSphere 6.5 -What’s New with vCenter 6.5?
What’s New with Virtual SAN 6.5? – New Features Overview
vSphere 6.5 -What’s New with vSphere 6.5 HA & DRS
vSphere 6.5 – What’s is in VMware vSphere 6.5 Fault Tolerance?
vSphere 6.5 – How VM’s are Secured using vSphere 6.5 Security Features?